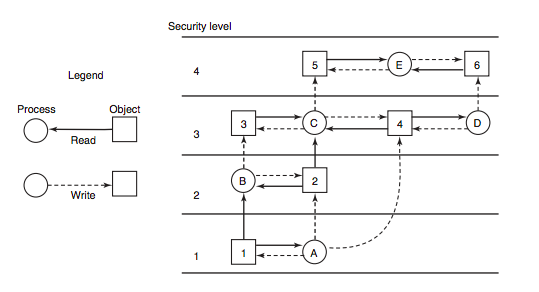
Figure 2.5 from Access control policies and companies data transmission management. (Gestion du contrôle de la diffusion des données d'entreprises et politiques de contrôles d'accès) | Semantic Scholar

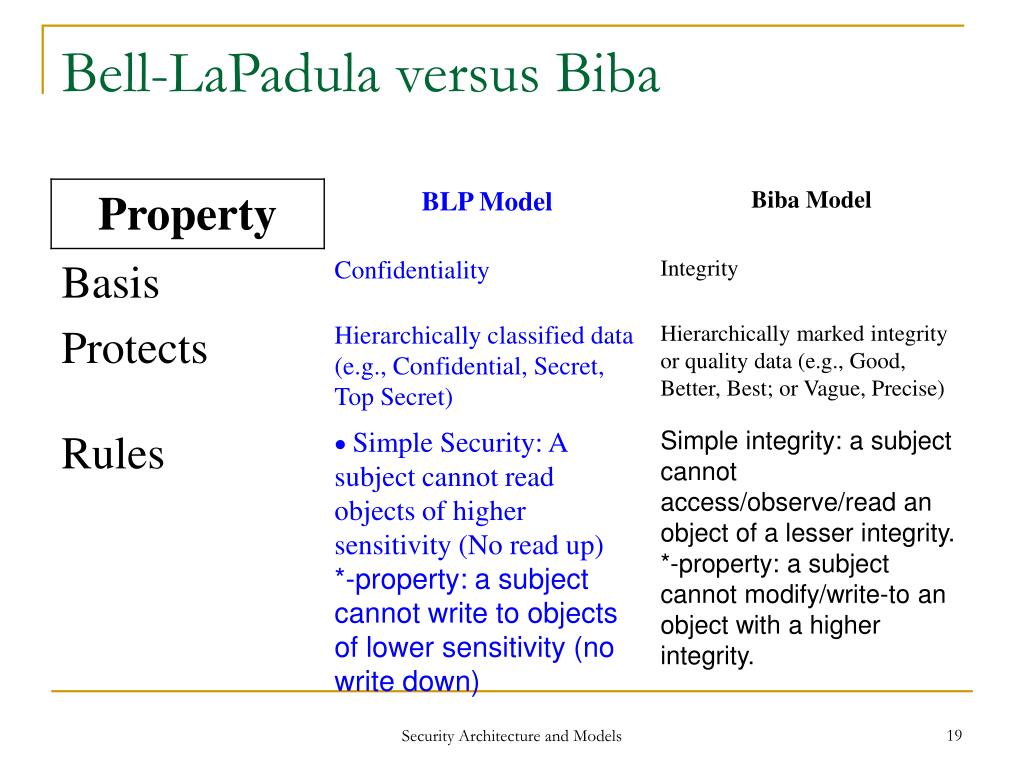
CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu
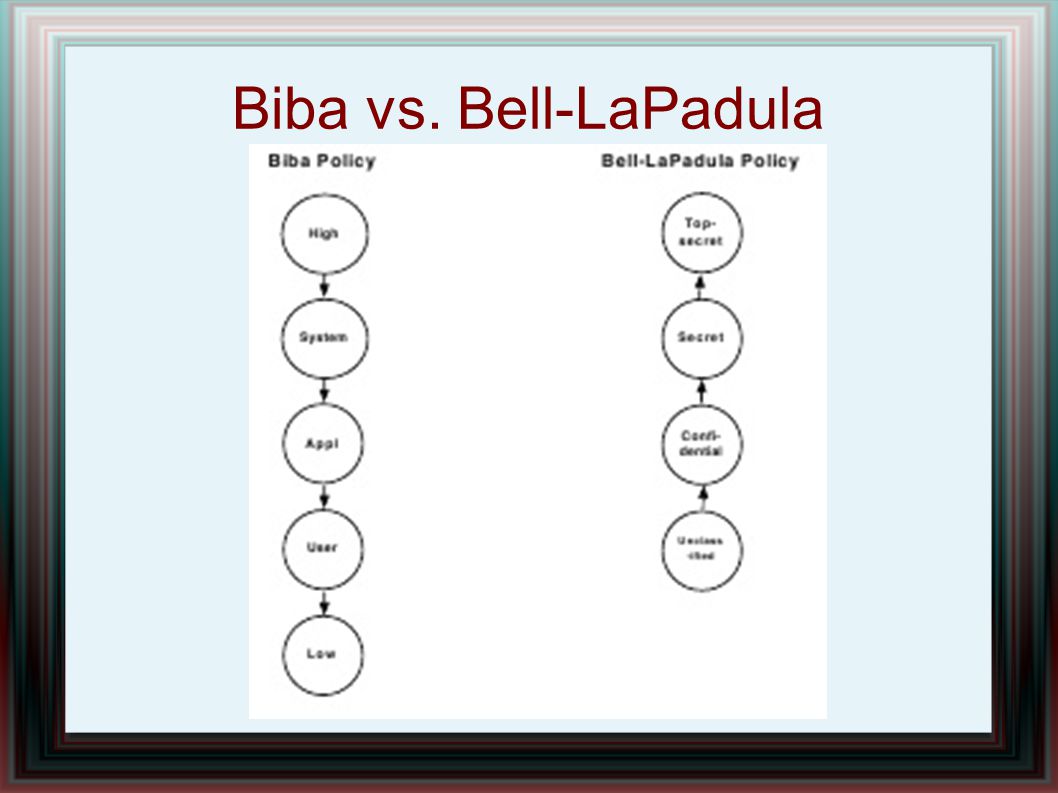
Evaluation of the Appropriateness of Trust Models to specify Defensive Computer Security Architectures for Physical Protection S